Table of Contents Link to heading
TrustSec Link to heading
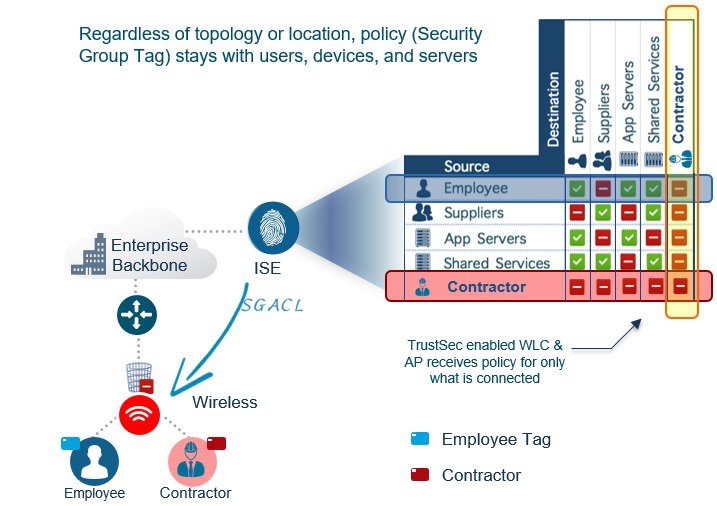
Cisco TrustSec (CTS) is a next-generation NAC solution that performs network enforcement by using Security Group Tags (SGTs) instead of IP addresses and ports.
SGT tags (dec/hex value) are assigned to authenticated groups of users or end devices. RBAC is enforced using SGACLs (Security Group ACLs), which match based on SGTs rather than IPs.
TrustSec configuration occurs in three phases:
Ingress Classification Link to heading
Dynamic assignment: The SGT is assigned dynamically when authenticating using 802.1x, MAB, or WebAuth.
Static assignment: In environments such as a data centre that do not require 802.1x, MAB, or WebAuth authentication. SGT tags can be statically mapped on SGT-capable network devices:
- IP to SGT tag
- Subnet to SGT tag
- VLAN to SGT tag
- Layer 2 interface to SGT tag
- Layer 3 logical interface to SGT tag
- Port to SGT tag
- Port profile to SGT tag
Propagation Link to heading
Inline tagging: Layer 2
- A switch inserts (native tagging) the SGT tag (16-bit) inside a frame.
- Supported only by Cisco network devices with ASIC support for TrustSec.
SGT Exchange Protocol (SXP) propagation: Layer 3
- A TCP-based peer-to-peer protocol used for non-inline tagging switches.
- IP-to-SGT mappings
Egress Enforcement Link to heading
Security Group ACL (SGACL):
- On routers and switches
- Filtered based on source and destination SGT tags
Security Group Firewall (SGFW):
- On Cisco Secure Firewalls
- Filtered based on tag-based rules
MACsec Link to heading
Traffic is encrypted only on the wire between two MACsec peers and is unencrypted as it is processed internally within the switch.
A 16-byte MACsec Security Tag field (802.1AE header) and a 16-byte Integrity Check Value (ICV) field are added to the frame.
MACsec provides authentication using Galois Message Authentication Code (GMAC) or authenticated encryption using Galois/Counter Mode Advanced Encryption Standard (AES-GCM).
Downlink MACsec Link to heading
Handled by the MACsec Key Agreement (MKA) keying protocol. This requires a MACsec-capable switch and a MACsec-capable supplicant on the endpoint (such as Cisco Secure Client).
Uplink MACsec Link to heading
By default, uplink MACsec uses Cisco proprietary Security Association Protocol (SAP) keying protocol. The encryption is the same AES-GCM-128 encryption used with both uplink and downlink MACsec.